KrakenD CE 2.13.4 and EE 2.13.2 update released
by Jorge Tarrero
This patch release of KrakenD Community Edition and Enterprise Edition upgrades the Golang version to 1.25.9 to address several disclosed CVEs. It also addresses CVE-2026-34986, which does not affect the KrakenD auth/validator component due to the lack of JWE support.
Additionally, this patch release includes KrakenD Enterprise fixes for the modifier/request-body-extractor, whose headers were not correctly propagated to the dynamic routing component, and a problem with Virtual Hosts feature that could expose URLs with internal __virtual path component.
Last but not least, it includes an important update to the XML encoder library, which, besides adding the latest bug fixes and improvements, significantly enhances performance when handling large response bodies. The previous XML encoder version performance was degraded as the data grew. The following graphs show the time improvements in seconds (Y-axis) versus the payload size in bytes (X-axis):
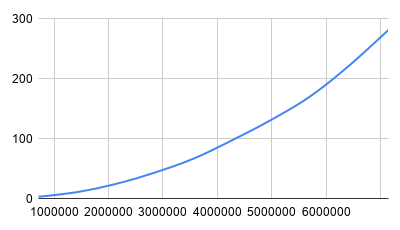
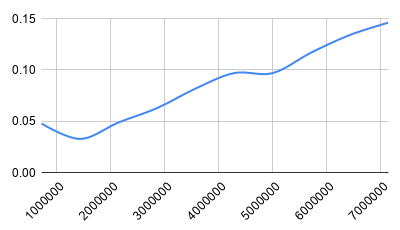
Now the response times are stable at millisecond marks, even with large data payloads
🚀 Summary of changes for EEv2.13.2 (patch)
Recommended security upgrade addressing several vulnerabilities and feature fixes
- Upgraded XML encoder with latest bug fixes and improvements, including a major overhaul in performance.
-
Fixed Virtual Hosts problem that could expose internal URLs with
__virtualpath component. -
Headers extracted using
modifier/request-body-extractorcomponent can now be used in dynamic routing. -
Upgraded
auth/validatorcomponent to address CVE-2026-34986 (false positive). - Upgraded Go to 1.25.9, addressing several CVEs with disclosed descriptions:
- CVE-2026-32283
crypto/tls: multiple key update handshake messages can cause connection to deadlock - CVE-2026-27140
cmd/go: trust layer bypass when using cgo and SWIG - CVE-2026-32280
crypto/x509: unexpected work during chain building - CVE-2026-32281
crypto/x509: inefficient policy validation - CVE-2026-32282
os: Root.Chmod can follow symlinks out of the root on Linux (false positive) - CVE-2026-32289
html/template: JS template literal context incorrectly tracked (false positive) - CVE-2026-27144
cmd/compile: no-op interface conversion bypasses overlap checking (false positive) - CVE-2026-27143
cmd/compile: possible memory corruption after bound check elimination (false positive) - CVE-2026-32288
archive/tar: unbounded allocation when parsing old format GNU sparse map (false positive)
- CVE-2026-32283
Upgrading to the latest version is always advised.
🚀 Summary of changes for CEv2.13.4 (patch)
Recommended security upgrade addressing several vulnerabilities and feature fixes
- Upgraded XML encoder with latest bug fixes and improvements, including a major overhaul in performance.
-
Upgraded
auth/validatorcomponent to address CVE-2026-34986 (false positive). - Upgraded Go to 1.25.9, addressing several CVEs with disclosed descriptions:
- CVE-2026-32283
crypto/tls: multiple key update handshake messages can cause connection to deadlock - CVE-2026-27140
cmd/go: trust layer bypass when using cgo and SWIG - CVE-2026-32280
crypto/x509: unexpected work during chain building - CVE-2026-32281
crypto/x509: inefficient policy validation - CVE-2026-32282
os: Root.Chmod can follow symlinks out of the root on Linux (false positive) - CVE-2026-32289
html/template: JS template literal context incorrectly tracked (false positive) - CVE-2026-27144
cmd/compile: no-op interface conversion bypasses overlap checking (false positive) - CVE-2026-27143
cmd/compile: possible memory corruption after bound check elimination (false positive) - CVE-2026-32288
archive/tar: unbounded allocation when parsing old format GNU sparse map (false positive)
- CVE-2026-32283
Upgrading to the latest version is always advised.